Trusted by Global Tech Leaders to Disruptive Startups
















Helping CTOs and CXOs Navigate Through Code Quality Challenges
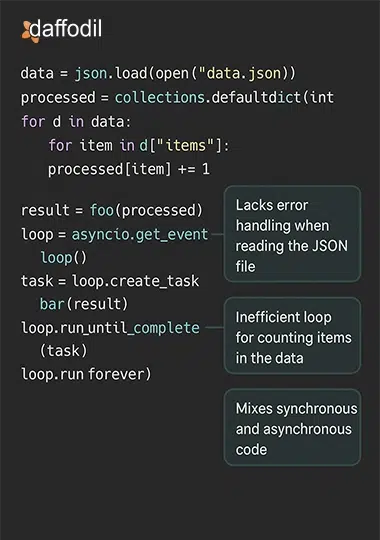
Our expert software developers analyze your existing codebase to identify technical debt, architectural flaws, and outdated practices. We provide actionable recommendations to modernize your code while preserving business logic and functionality.
Our systematic code audit process identifies security vulnerabilities that might otherwise remain hidden until exploited. Our security-focused code reviews detect potential vulnerabilities, SQL injection risks, and authentication issues that automated tools often miss.
By establishing consistent coding standards and best practices, we help your development team work more efficiently. Our reviews provide educational feedback that builds skills and reduces time spent on debugging and refactoring.
Our comprehensive code review services identify redundancies, inefficiencies, and maintenance challenges that accumulate as technical debt. We help prioritize improvements that will yield the greatest return on development investment.
Through detailed performance analysis, we identify bottlenecks and optimization opportunities in your code. Our recommendations help streamline execution, improve responsiveness, and enhance the user experience.
Our code reviews evaluate how well your applications will function across different environments and at scale. We help you build robust solutions that perform consistently regardless of platform, device, or user load.
Turnkey Software Code Review Services
Ensure that your software meets the industry standards
Get a no-obligation consultingCustomer Sucess Stories
See What Our Clients Have to Say

Richard Valway
Owner, Brimstone Allon Enterprises, LLC
““Their supplemental work has enhanced both the speed and quality of our development. Their depth and breadth of resources is impressive. Daffodil Software has the ability to get us anything we need; they serve as a full-service development shop.””

Sachin Singh
Founding Member & CTO, Fabulate
““With our previous developers, we were spending as much as 30% of our efforts fixing bugs before a release. Now, with Daffodil, we only spend around 3%—an enormous improvement. They’ve provided us with a dedicated team that really looks after us and our problems. Even in instances when we’ve had to push them hard, they were flexible enough to work late night...”
Mark Kozak
Co-Founder, MayaMD

Oluwatosin Odunlami
CEO, GoKonnect Interactive Media
““Despite encountering issues with the existing code, they maneuvered well around stumbling blocks and rewarded us with high-quality solutions, which we didn’t get from the previous team we worked with. They met both our deadlines and requirements satisfactorily, accommodating all our team’s change requests throughout the process.””

Nico Roberts
CEO, Rootery
““We’ve been in this market for a while, and they’re by far the most cost-effective. Their team and customer service are top-notch. We’re a startup that changes our mind often, and they’ve been able to adapt quickly.””
James Nieman
Creator and Founder, Sorta Jobs

Richard Valway
Owner, Brimstone Allon Enterprises, LLC
““Their supplemental work has enhanced both the speed and quality of our development. Their depth and breadth of resources is impressive. Daffodil Software has the ability to get us anything we need; they serve as a full-service development shop.””

Sachin Singh
Founding Member & CTO, Fabulate
““With our previous developers, we were spending as much as 30% of our efforts fixing bugs before a release. Now, with Daffodil, we only spend around 3%—an enormous improvement. They’ve provided us with a dedicated team that really looks after us and our problems. Even in instances when we’ve had to push them hard, they were flexible enough to work late night...”
Mark Kozak
Co-Founder, MayaMD

Oluwatosin Odunlami
CEO, GoKonnect Interactive Media
““Despite encountering issues with the existing code, they maneuvered well around stumbling blocks and rewarded us with high-quality solutions, which we didn’t get from the previous team we worked with. They met both our deadlines and requirements satisfactorily, accommodating all our team’s change requests throughout the process.””

Nico Roberts
CEO, Rootery
““We’ve been in this market for a while, and they’re by far the most cost-effective. Their team and customer service are top-notch. We’re a startup that changes our mind often, and they’ve been able to adapt quickly.””
James Nieman
Creator and Founder, Sorta Jobs
Future-Proof Your Software. Get a quote now!
Contact NowEnsure Excellent Code Quality With our Stringent Code Audit Process

Step 1: Discovery and Requirement Analysis
- Conduct comprehensive stakeholder interviews to understand specific needs and objectives
- Examine project documentation, technology stack, and business requirements
- Identify pain points, challenges, and goals specific to your application
- Discuss current development practices and team organization
- Establish clear audit parameters and success criteria
Step 2: Comprehensive Code Analysis
- Deploy automated scanning tools customized for your technology stack
- Identify syntax errors, code smells, and potential bugs through static analysis
- Conduct a manual review of critical components and architectural decisions
- Evaluate code organization, modularity, and adherence to best practices
- Assess documentation quality and completeness within the codebase
- Review test coverage and effectiveness of existing unit/integration tests
Step 3: Performance Testing and Security Assessment
- Measure application performance under various load conditions
- Identify bottlenecks in code execution, database queries, and API calls
- Evaluate memory usage, CPU utilization, and resource consumption patterns
- Conduct security vulnerability scanning and penetration testing
- Assess authentication mechanisms, data validation, and encryption implementation
- Verify compliance with relevant industry regulations and standards
Step 4: Findings Compilation and Recommendation Development
- Document all discovered issues with clear technical details
- Categorize findings by type, severity, and impact on business objectives
- Prioritize issues based on risk assessment and remediation complexity
- Develop practical, actionable recommendations for each finding
- Create estimated effort projections for implementing solutions
- Compile a comprehensive report balancing technical detail with clear explanations
Step 5: Knowledge Transfer and Implementation Support
- Present detailed findings and recommendations to your development team
- Conduct interactive sessions to answer questions and clarify technical details
- Help develop a prioritized remediation roadmap aligned with your capacity
- Provide guidance on implementing best practices and coding standards
- Offer training sessions on security awareness and performance optimization
- Provide ongoing support during the implementation of recommended changes
(item.title)+×
(item.content) && (- Conduct comprehensive stakeholder interviews to understand specific needs and objectives
- Examine project documentation, technology stack, and business requirements
- Identify pain points, challenges, and goals specific to your application
- Discuss current development practices and team organization
- Establish clear audit parameters and success criteria
(item.title)+×
(item.content) && (- Deploy automated scanning tools customized for your technology stack
- Identify syntax errors, code smells, and potential bugs through static analysis
- Conduct a manual review of critical components and architectural decisions
- Evaluate code organization, modularity, and adherence to best practices
- Assess documentation quality and completeness within the codebase
- Review test coverage and effectiveness of existing unit/integration tests
(item.title)+×
(item.content) && (- Measure application performance under various load conditions
- Identify bottlenecks in code execution, database queries, and API calls
- Evaluate memory usage, CPU utilization, and resource consumption patterns
- Conduct security vulnerability scanning and penetration testing
- Assess authentication mechanisms, data validation, and encryption implementation
- Verify compliance with relevant industry regulations and standards
(item.title)+×
(item.content) && (- Document all discovered issues with clear technical details
- Categorize findings by type, severity, and impact on business objectives
- Prioritize issues based on risk assessment and remediation complexity
- Develop practical, actionable recommendations for each finding
- Create estimated effort projections for implementing solutions
- Compile a comprehensive report balancing technical detail with clear explanations
(item.title)+×
(item.content) && (- Present detailed findings and recommendations to your development team
- Conduct interactive sessions to answer questions and clarify technical details
- Help develop a prioritized remediation roadmap aligned with your capacity
- Provide guidance on implementing best practices and coding standards
- Offer training sessions on security awareness and performance optimization
- Provide ongoing support during the implementation of recommended changes
Step 1: Discovery and Requirement Analysis
- Conduct comprehensive stakeholder interviews to understand specific needs and objectives
- Examine project documentation, technology stack, and business requirements
- Identify pain points, challenges, and goals specific to your application
- Discuss current development practices and team organization
- Establish clear audit parameters and success criteria
Step 2: Comprehensive Code Analysis
- Deploy automated scanning tools customized for your technology stack
- Identify syntax errors, code smells, and potential bugs through static analysis
- Conduct a manual review of critical components and architectural decisions
- Evaluate code organization, modularity, and adherence to best practices
- Assess documentation quality and completeness within the codebase
- Review test coverage and effectiveness of existing unit/integration tests
Step 3: Performance Testing and Security Assessment
- Measure application performance under various load conditions
- Identify bottlenecks in code execution, database queries, and API calls
- Evaluate memory usage, CPU utilization, and resource consumption patterns
- Conduct security vulnerability scanning and penetration testing
- Assess authentication mechanisms, data validation, and encryption implementation
- Verify compliance with relevant industry regulations and standards
Step 4: Findings Compilation and Recommendation Development
- Document all discovered issues with clear technical details
- Categorize findings by type, severity, and impact on business objectives
- Prioritize issues based on risk assessment and remediation complexity
- Develop practical, actionable recommendations for each finding
- Create estimated effort projections for implementing solutions
- Compile a comprehensive report balancing technical detail with clear explanations
Step 5: Knowledge Transfer and Implementation Support
- Present detailed findings and recommendations to your development team
- Conduct interactive sessions to answer questions and clarify technical details
- Help develop a prioritized remediation roadmap aligned with your capacity
- Provide guidance on implementing best practices and coding standards
- Offer training sessions on security awareness and performance optimization
- Provide ongoing support during the implementation of recommended changes
Why Daffodil Software
Recognized excellence. proven customer satisfaction
25+
Years Of Software Engineering Excellence
150+
Global Clientele
4.8
Avg CSAT Score
95%
Customer Retention Rate
1000+
Software Engineering Experts
50+
Subject Matter Experts
Tools And Technologies We Excel In
Daffodil has been an early adopter of emerging technologies and has built extensive experience in various programming languages, frameworks, libraries, and tools. We continuously experiment with new technologies through our in-house R&D labs and pass on the learnings to our clients for a competitive edge.